Another difficult time for Skype users. Recently, a malware was found targeting Skype users. This malware, known as T9000, captures the victim’s screenshots and his whole conversation. But, there is one unique thing about this malware. Instead of targeting all Skype users, its target is specific. Automotive industry, human right activists, and governments are the only known targets. Moreover, all targets share one thing in common. They are all in Asia Pacific region. This is when we call it ‘weird.’
The malware was first spotted by Palo Alto Networks security researchers. The attackers hide the malware inside an RTF attachment. Even if the security system recognizes the email as malicious, it will end as a common phishing attempt. The real threat is still hidden deep down there. It waits for the time to get into the system. Once in, all Skype users will be affected.
Compare to its predecessor, T9000 has a much complex structure. It exists to avoid detection. Before installing itself, it scans your system for security system. It can recognize the following security products:
- Sophos
- Baidu
- Gdata
- INCAInternet
- Comodo
- DoctorWeb
- AVG
- TrustPortAntivirus
- VirusChaser
- BitDefender
- Panda
- Trend Micro
- McAfee
- Norton
- Kingsoft
- Filseclab
- Micropoint
- JiangMin
- AhnLab
- Avira
- Tencent
- Rising
- Kaspersky
- Qihoo 360
- Any malware analysis tool
How T9000 Attacks Skype Users
The scanning process will make sure your system is ‘clean.’ Then, the internal verification will proceed. This step prepares everything for the installation process. Once the malware entered your system, it will collect your information. All information will be sent to a C&C server. At this point, using a server is important. The attacker use it not only to store Skype users data, but also distinguish every victim. Without it, it will be difficult to choose the target. Next, the attacker will choose the victims. It can be anyone. Once he came with the name, the server will send instructions based on the victim’s personal information.
To attack Skype users, T9000 use 3 main modules.
- tyeu.dat
- vnkd.dat
- qhnj.dat
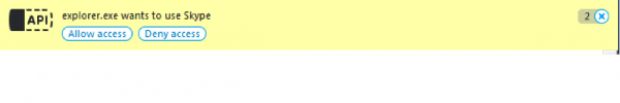 If you got this message, be careful. T9000 backdoor has successfully tapped into your Skype API. For your last effort, please don’t allow the access. If you do it, the attacker will get full access to your system. He can spy on you whenever he wants. The end. You will lose your information. The attacker will get all your video, text, and audio chats. The attacker can even take screenshots of your conversation. So, before that happens, make sure you don’t click that button.
If you got this message, be careful. T9000 backdoor has successfully tapped into your Skype API. For your last effort, please don’t allow the access. If you do it, the attacker will get full access to your system. He can spy on you whenever he wants. The end. You will lose your information. The attacker will get all your video, text, and audio chats. The attacker can even take screenshots of your conversation. So, before that happens, make sure you don’t click that button.A Strategic Malware Attack
“To further protect our customers, we’ve added detection for the malicious software known as ‘T9000’ to Windows Defender. Customers that have installed security updates released in 2012 (MS12-060) and 2014 (MS14-033), either manually or by enabling automatic updates, will already be protected. Our recommendation is to enable automatic updates, which installs the latest security protections, and use the latest version of Skype.”
 English
English
 German
German Dutch
Dutch Thai
Thai Chinese
Chinese